- Welcome to CodeWalrus.
Recent posts
#91
Calc Projects, Programming & Tutorials / Re: HASHLIB - Cryptography Lib...
Last post by ACagliano - April 15, 2022, 03:20:10 AMUpdate and API revision
HASHLIB's API got a bit of a facelift recently with the function set changing nomenclature depending on what function is being served by the group of functions. No longer are hashlib functions prefixed with hashlib_, they are prefixed with a class-esque namespace indicating what they do. Like so:
Invocations of the Secure RNG within HASHLIB look like this:
The latest update is available here.
The header has some slight issues in the documentation... stay tuned for a 9.1 update for a fix, but everything works as of v9.
https://github.com/acagliano/hashlib/releases/latest
I am also opening the floor if anyone wants to contribute hashing algorithms. Fast hashes like sha512, sha1 welcome, as well as slower hashes like argon.
HASHLIB's API got a bit of a facelift recently with the function set changing nomenclature depending on what function is being served by the group of functions. No longer are hashlib functions prefixed with hashlib_, they are prefixed with a class-esque namespace indicating what they do. Like so:
Invocations of the Secure RNG within HASHLIB look like this:
Code Select
csrand_init(); initializes the entropy source internally
csrand_get(); returns a random 32-bit unsigned int
csrand_fill(); fills a buffer to a size with random bytes
Invocations of Hashing look like this:Code Select
hash_ctx hash;
uint8_t out[32];
hash_init(&hash, ALG_NAME) initializes a context of type ALG_NAME
hash_update(&hash, data, len)
hash_final(&hash, out)
hash_mgf1(..., ALG_NAME)
/* Due to the structure of the hash context, the following are
viable alternatives to hash_update and hash_final:
uint8_t out[32];
hash_ctx hash;
hash_init(&hash, SHA256);
hash.update(&hash.Hash, data, len);
hash.final(&hash.Hash, out);
Invocations of HMAC are set up and have the same alternatives as hashing:Code Select
hmac_init()
hmac_update()
hmac_final()
hmac_pbkdf2(..., ALG_NAME)
The AES cipher is invoked like so:Code Select
aes_loadkey()
aes_encrypt()
aes_decrypt()
The RSA cipher is invoked like so:Code Select
rsa_encrypt()
// The RSA encryptor takes a hash ID specifier so that, if other hashes
// are added at some point, they can be used with OAEP internal to RSA.
Digest operations look like this:Code Select
digest_tostring()
digest_compare()
The latest update is available here.
The header has some slight issues in the documentation... stay tuned for a 9.1 update for a fix, but everything works as of v9.
https://github.com/acagliano/hashlib/releases/latest
I am also opening the floor if anyone wants to contribute hashing algorithms. Fast hashes like sha512, sha1 welcome, as well as slower hashes like argon.
#92
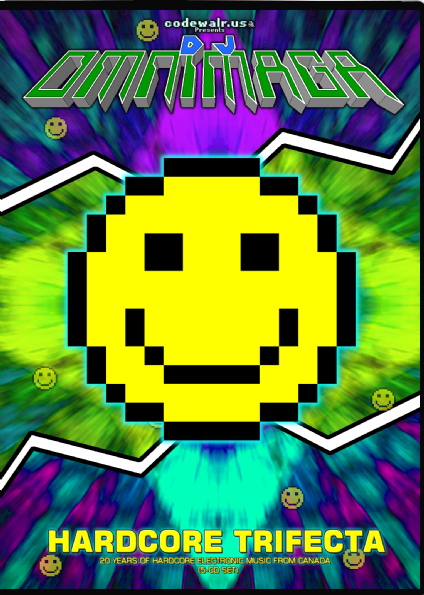
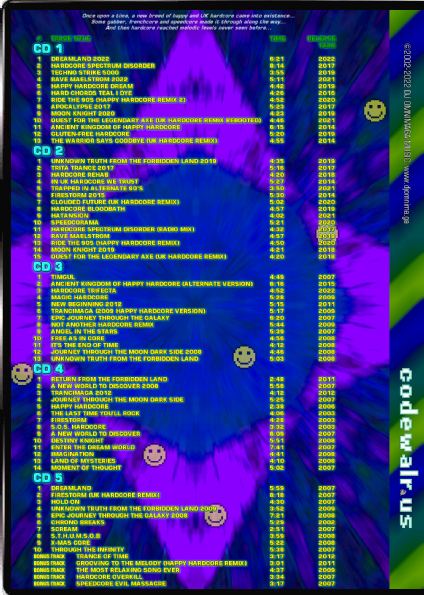
Music Showcase & Production with other softwares / Re: Hardcore Trifecta, Hatansi...
Last post by Dream of Omnimaga - April 01, 2022, 03:55:19 PMThere is now a ballad version of Hardcore Trifecta song: https://djomnimaga.bandcamp.com/track/track-ballad-trifecta
And no this one doesn't go berserk.
And no this one doesn't go berserk.
#93
Games / Re: [HP Prime] Supersonic Ball...
Last post by Dream of Omnimaga - April 01, 2022, 03:36:07 PMNot sure why I didn't post this but the game has been finished a while ago and is now available for download in the first post. Among new features there are multiple themes with different tilesets and colors.


#94
Music Showcase & Production with other softwares / Hardcore Trifecta, Hatansion p...
Last post by Dream of Omnimaga - March 28, 2022, 04:56:34 PMI am currently in the process of preparing three releases, one of which is already available in the first post, but I'll make another post later with a copy of the URL and my landing page. Here are the releases in the works:
-Hatansion: Physical CD release in jewel case. Digital release available with bonus track in previous post.
-Another Decade of Magic Hardcore (2013-2022): Digital compilation release (includes all hardcore genre songs from the aforementioned album)

-Hardcore Trifecta: 20 Years of Magic Hardcore: Physical release only. It is currently available at https://www.trepstar.com/purchase.asp?idpub=62740&mode=all (it's a DVD case with 5 CD's in it)
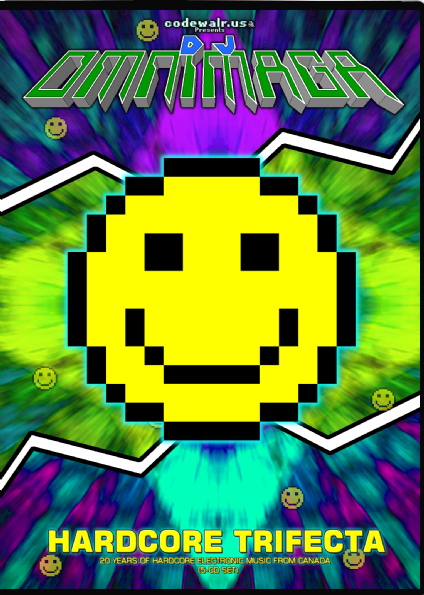
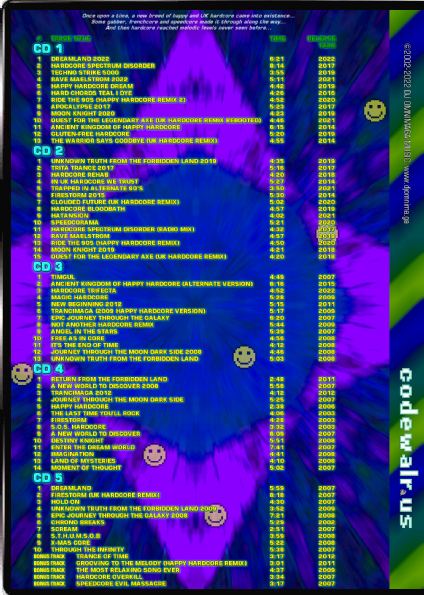
Hardcore Trifecta is essentially both my hardcore compilations (including Another Decade of Magic Hardcore (2013-2022), which comes out in April on the 10th anniversary of its predecessor) combined together with 5 bonus tracks.
Here are my newest songs (some of which are not hardcore):
https://djomnimaga.bandcamp.com/track/dreamland-2022
https://djomnimaga.bandcamp.com/track/old-macdonald-had-a-metal-farm
https://djomnimaga.bandcamp.com/track/hatansion
https://djomnimaga.bandcamp.com/track/dont-let-him-laugh-32-bit-version-2
https://djomnimaga.bandcamp.com/track/the-victors-of-the-north-extended-eurodance-remix
https://djomnimaga.bandcamp.com/track/rave-maelstrom-2022
-Hatansion: Physical CD release in jewel case. Digital release available with bonus track in previous post.
-Another Decade of Magic Hardcore (2013-2022): Digital compilation release (includes all hardcore genre songs from the aforementioned album)

-Hardcore Trifecta: 20 Years of Magic Hardcore: Physical release only. It is currently available at https://www.trepstar.com/purchase.asp?idpub=62740&mode=all (it's a DVD case with 5 CD's in it)
Hardcore Trifecta is essentially both my hardcore compilations (including Another Decade of Magic Hardcore (2013-2022), which comes out in April on the 10th anniversary of its predecessor) combined together with 5 bonus tracks.
Here are my newest songs (some of which are not hardcore):
https://djomnimaga.bandcamp.com/track/dreamland-2022
https://djomnimaga.bandcamp.com/track/old-macdonald-had-a-metal-farm
https://djomnimaga.bandcamp.com/track/hatansion
https://djomnimaga.bandcamp.com/track/dont-let-him-laugh-32-bit-version-2
https://djomnimaga.bandcamp.com/track/the-victors-of-the-north-extended-eurodance-remix
https://djomnimaga.bandcamp.com/track/rave-maelstrom-2022
#95
Games / Re: [TI-84+CE] Opossum Massage...
Last post by Dream of Omnimaga - March 20, 2022, 10:42:53 AMThe game has now been ported to the HP Prime! https://tiplanet.org/forum/archives_voir.php?id=2871782
#96
Music Showcase & Production with other softwares / Hatansion, DJ Omnimaga's 15th ...
Last post by Dream of Omnimaga - February 28, 2022, 10:41:42 AMToday I am pleased to announce the release of my 15th studio album: Hatansion!

This new album includes eurodance, happy hardcore, UK hardcore, frenchcore, italo disco and electronic power metal remixes of songs that I made before, as well as cover songs of two public domain songs and two new ones. I hope that you enjoy.
Download and streaming links: https://linktr.ee/djomnimaga

This new album includes eurodance, happy hardcore, UK hardcore, frenchcore, italo disco and electronic power metal remixes of songs that I made before, as well as cover songs of two public domain songs and two new ones. I hope that you enjoy.

Download and streaming links: https://linktr.ee/djomnimaga
#97
Games / [HP Prime] Supersonic Ball HP
Last post by Dream of Omnimaga - February 25, 2022, 01:47:11 AMThis is an HP Prime remake of my TI-83 Plus game Supersonic Ball. For speed reasons a G2 calculator model is recommended but it should still be somewhat playable on G1 models. I still need to finish some touches and optimize this to hopefully increase speed. The latest feature I added is the ability to play the game at calc speed even on the emulator and on the emulator you can now press mem to slow the game down x10 for smoother animated capture on slower computers (you just have to speed up the video in an editor afterward).
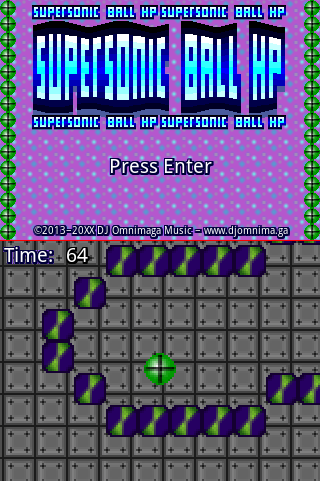

Download link:
https://www.cemetech.net/downloads/files/2227
https://tiplanet.org/forum/archives_voir.php?id=2867577

Download link:
https://www.cemetech.net/downloads/files/2227
https://tiplanet.org/forum/archives_voir.php?id=2867577
#98
Calc Projects, Programming & Tutorials / Re: HASHLIB - Cryptography Lib...
Last post by ACagliano - February 06, 2022, 03:34:52 AMQuote from: DJ Omnimaga on February 05, 2022, 06:27:57 PMI'm glad to see this worked on stillTI-Trek does actually use HASHLIB for login, and TI-Trek is actually my method of testing it. TI-Trek's login process is like so:, I wonder how much of this will be of use for your other project TI-Trek? (eg server credentials)
- Users register on the web deck (website). Doing so generates them a login token, which is a PBKDF2 key exported into an appvar. They place that appvar on their calculator.
- Running the game with that appvar present imports the key to user settings and deletes the keyfile.
- Login to the Trek server causes the server to generate an RSA keypair. The length of the key is configurable between 1024 and 2048. The public key is sent to the calculator. The public exponent is the standard 65537.
- The calculator uses the SPRNG to generate an AES key that is 256-bits long. That key is encrypted with RSA and sent to the server.
- The server decrypts that key and sets up an AES session.
- The calculator AES-encrypts the login token, which the server decrypts to authenticate the user. An account with a matching token is logged into.
- The AES session is then destroyed.
But even apart from TI-Trek, I'm hoping other people will find use of this too. It certainly is of significant use to anyone doing networking who needs secure channels.
#99
Calc Projects, Programming & Tutorials / Re: HASHLIB - Cryptography Lib...
Last post by Dream of Omnimaga - February 05, 2022, 06:27:57 PMI'm glad to see this worked on still  , I wonder how much of this will be of use for your other project TI-Trek? (eg server credentials)
, I wonder how much of this will be of use for your other project TI-Trek? (eg server credentials)
 , I wonder how much of this will be of use for your other project TI-Trek? (eg server credentials)
, I wonder how much of this will be of use for your other project TI-Trek? (eg server credentials) #100
Calc Projects, Programming & Tutorials / Re: HASHLIB - Cryptography Lib...
Last post by ACagliano - February 05, 2022, 04:50:00 PM- An eighth release of HASHLIB is now available for download. It adds two new implementations as well as some side-channel resistance enhancements. The new library release offers the following:
- A hardware-based secure RNG
- SHA-256 hash
- SHA-256 HMAC
- SHA-256 MGF1
- PBKDF2 via SHA-256 HMAC
- Advanced Encryption Standard (AES), for 128, 192, and 256 bit keys
- automatic application and stripping of preferred AES padding schemes (ISO-9797 M2 or PKCS#7), where applicable
- RSA public key encryption for public modulus between 1024 and 2048 bits
- Automatic application and stripping of RSAEP-OAEP via PKCS#1 v2.2
- Authentication of SSL certificates signed with RSA with SHA-256
- Digest comparison function resistant to timing analysis
- Digest to hex-string function
- All user-facing encryptor functions zero all memory from the start of the current stack frame to the bottom of the stack before handing back control, to prevent state leak.
- All user-facing encryptor functions disable interrupts while running, which prevents the OS from responding to USB activity. This serves to stop attempts to map the contents of the device memory while sensitive functions are running.
In addition, the following measures were taken for side channel resistance:
In addition, the documentation is split into a "Quick Reference" for general assistance, and a Cryptanalysis that provides more technical details (for peer-review).
HASHLIB is still under analysis and peer-review to continue to harden it. Feel free to contribute suggestions for this.
https://github.com/acagliano/hashlib/releases/latest
Powered by EzPortal


